Deploying Chromebook agent via Google Admin console
Prerequisites
- Review the Requirements.
- Google Enterprise subscription. This is required in order to securely deploy the agent and prevent users from removing it from their device. A trial version is available.
- Access to the Unified Security Service Chromebook app. This is required during the early access stage. Please contact your service provider for further information.
- If you require separation of configurations for users in your directory it is recommended that you create an Organizational Unit and add any users that will use the Chromebook agent to the OU. This is optional, you could instead use the top-level OU however access and configuration of the USS Agent will apply to all users in the organization.
- Administrator access to the Google Admin console.
- Administrator access to the USS Dashboard.
- If the Chromebook you are installing on is new, please log in and install the Google Play service before proceeding to deploy the Chromebook agent using this guide.
Deployment Steps
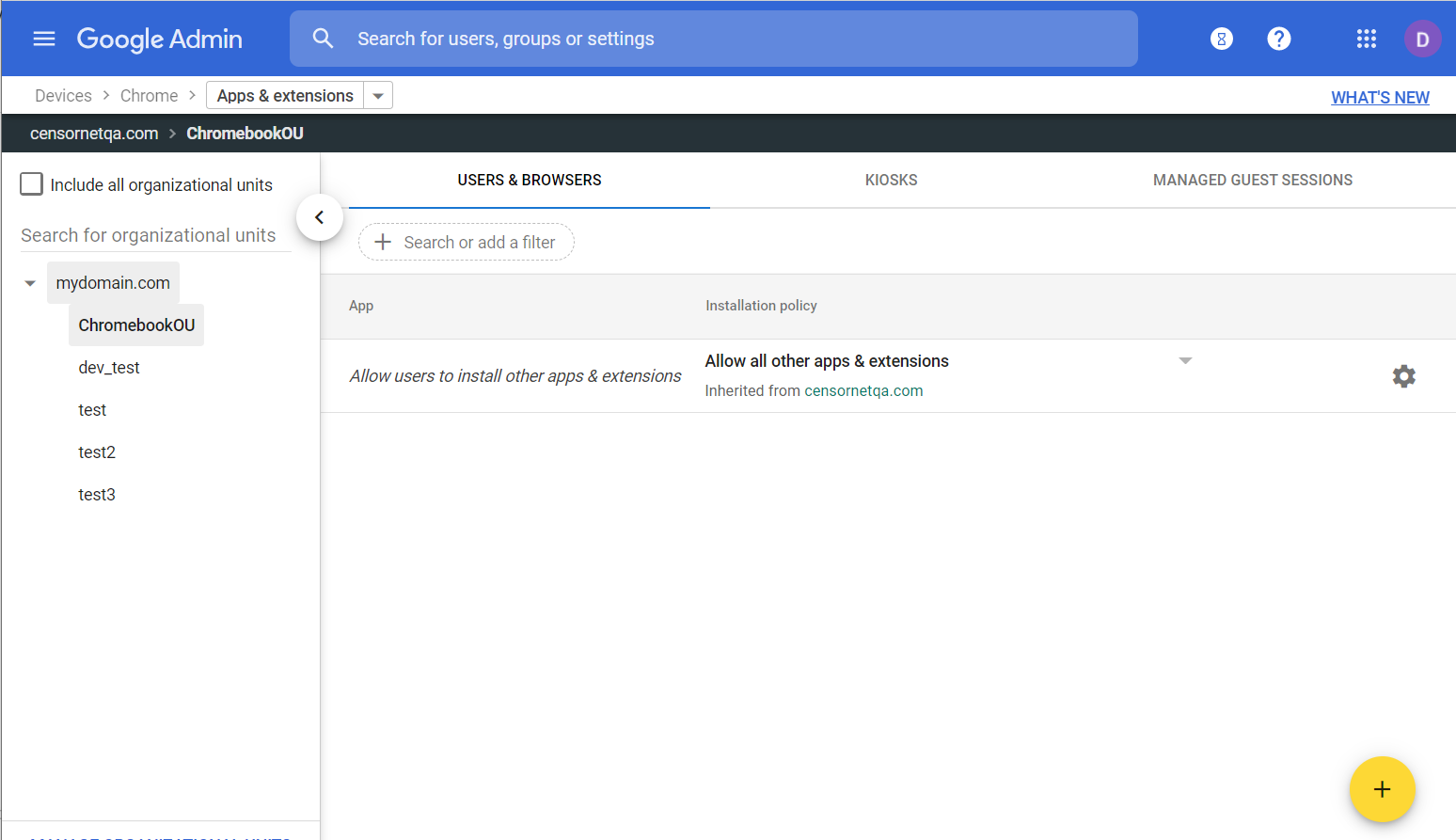
- Sign in to the Google Admin console
- From the left menu, select Devices, then Chrome, then Apps & Extensions and then Users & Browsers.
- Select the desired Organizational Unit from the list on the left.
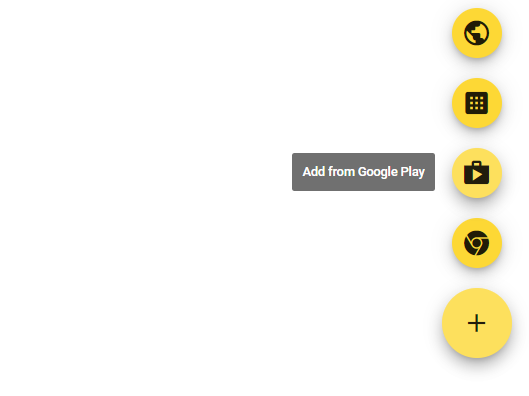
- Click the yellow + icon and then Add from Google Play
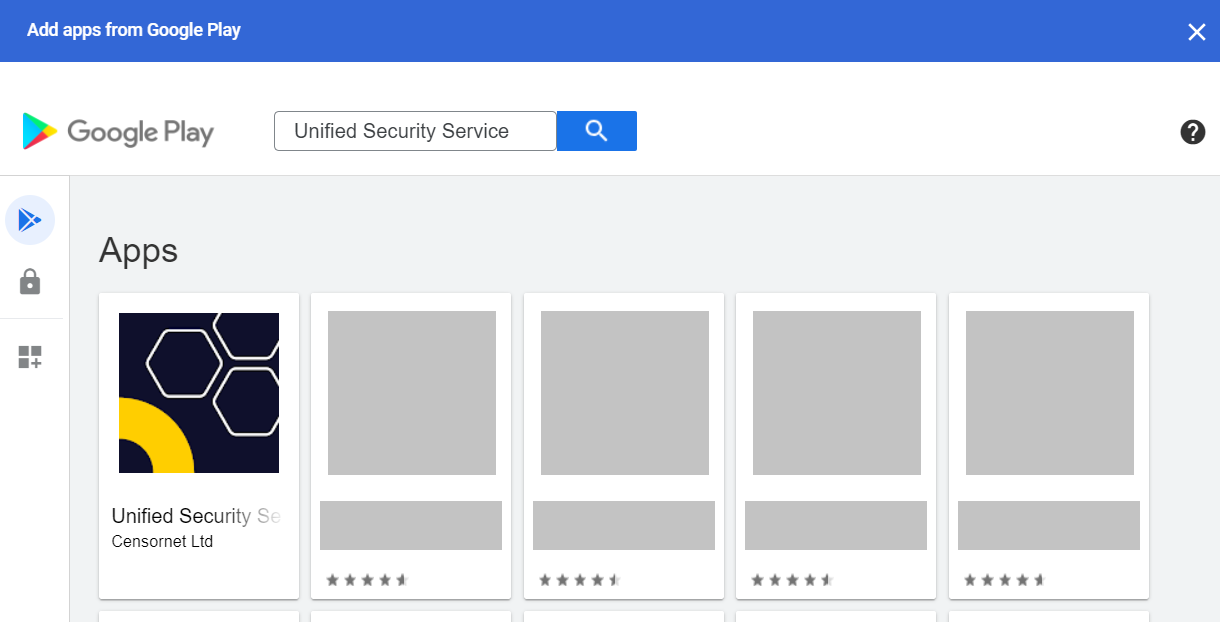
- In the Add apps from Google Play dialog search for Unified Security Service. It should appear as the first tile in the list.
- Click the tile to view the app information and confirm the app is Approved
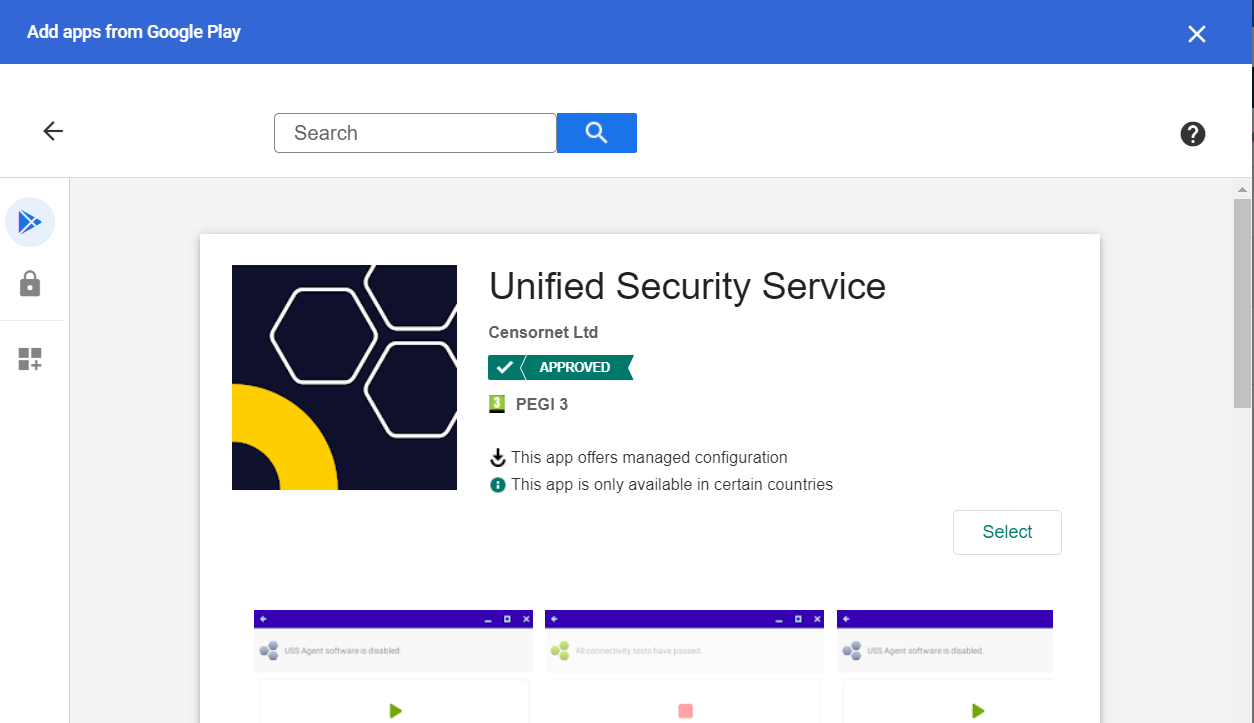
- Click the Select button on the right hand center of the window. The app will be added to the list of available apps in Users & Browsers.
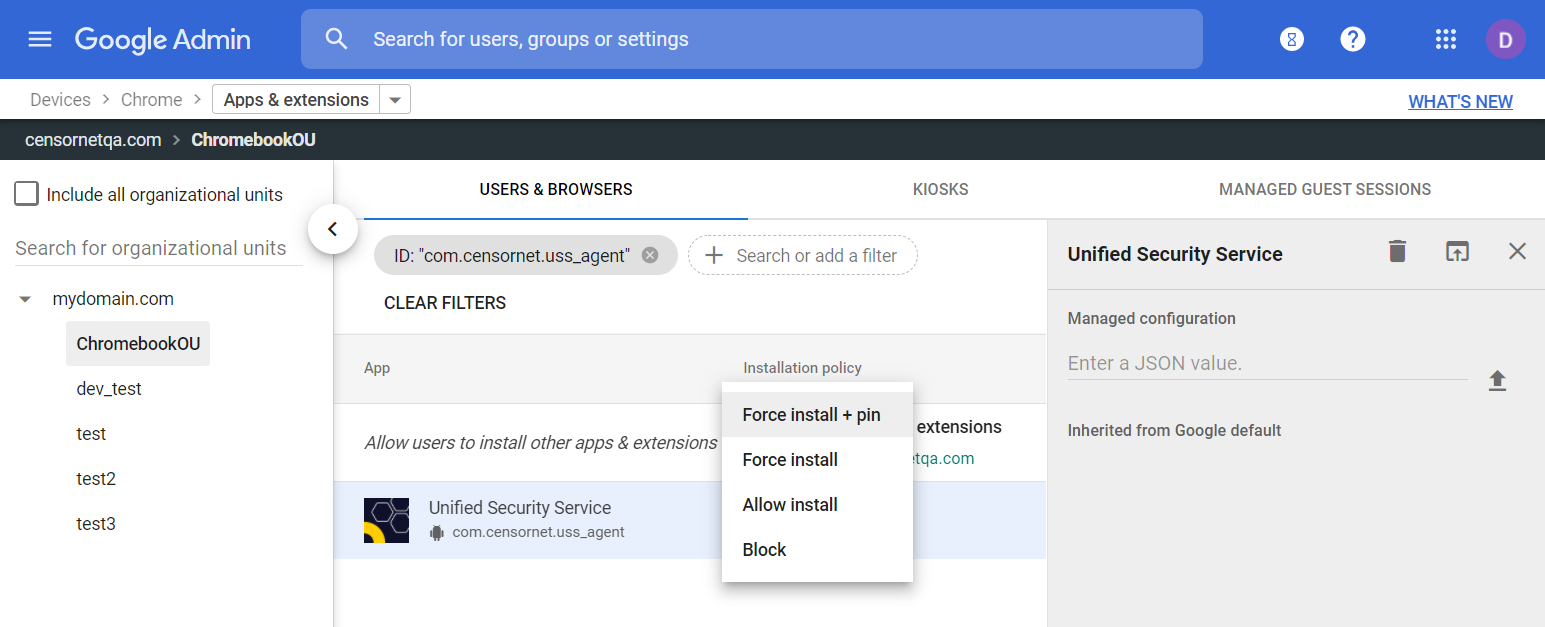
- Change the Allow Install menu option to Force Install or Force Install + Pin depending on your preference (see the Google Deployment Guide for more information). Note that "Pin" in this context means to pin the app to the task bar, rather than a security pin code.
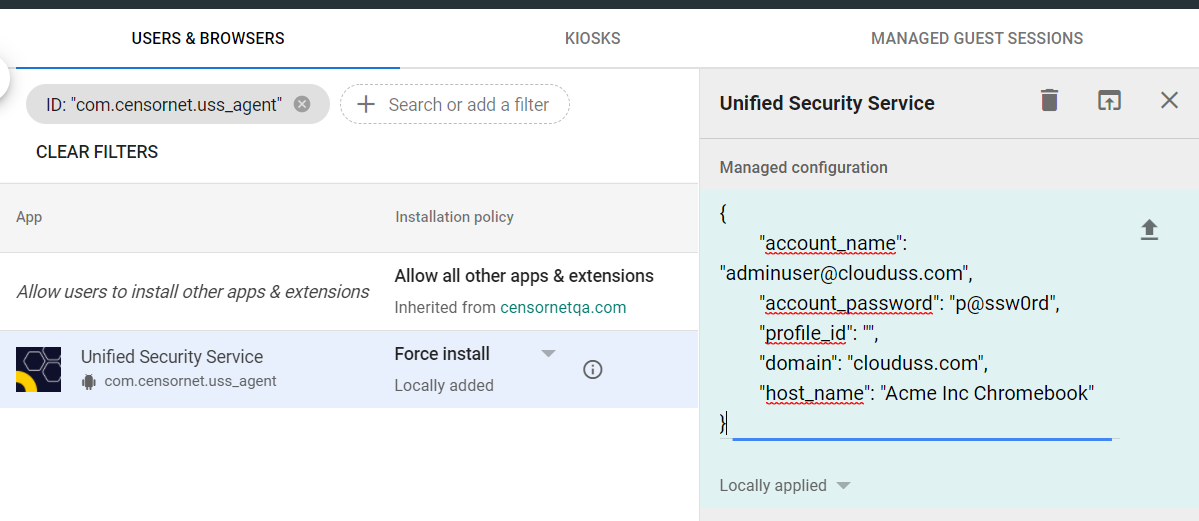
- In the right hand panel (click the app listing if it is not open already), paste in the following JSON template after updating the placeholder values:
adminuser@clouduss.com and p@assw0rd with the real credentials for a USS administrator user with at least the Agent Installer role applied.{
"account_name": "adminuser@clouduss.com",
"account_password": "p@ssw0rd",
"profile_id": "",
"domain": "clouduss.com",
"host_name": "Acme Inc Chromebook"
}
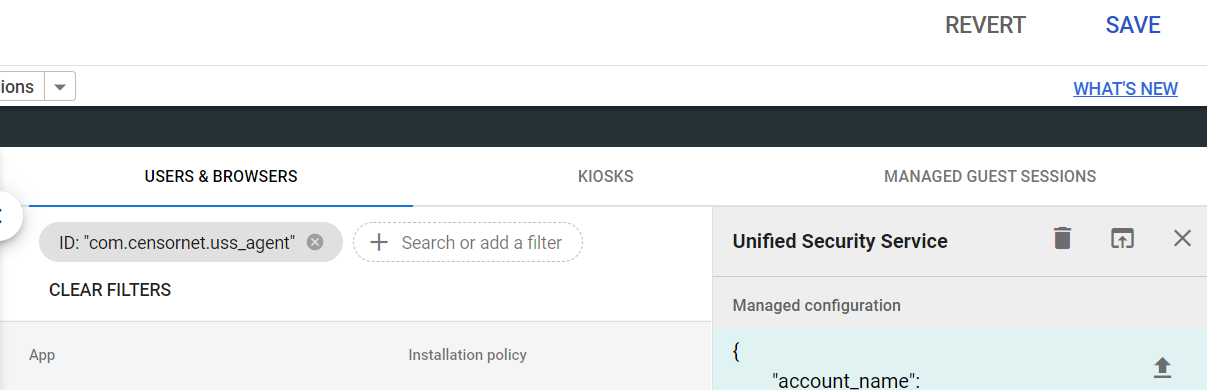
- Click the Save button in the top right of the window
- Navigate to Devices, then Chrome, then Settings and Users & Browsers. Ensure your OU is still selected and then search for "proxy":
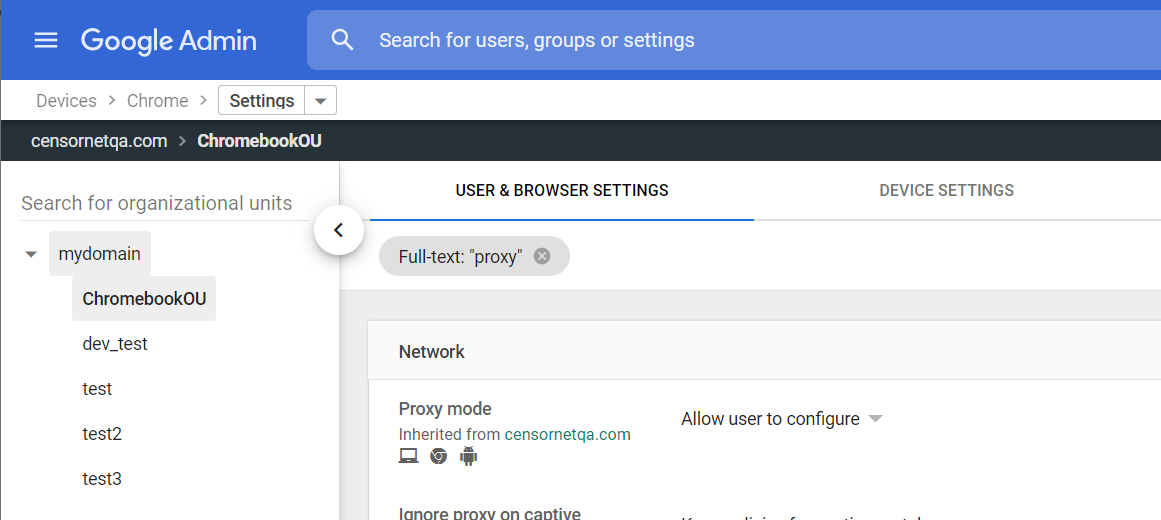
- In the Proxy Mode option from the Network section, change the value to Always use the proxy auto-config specified below
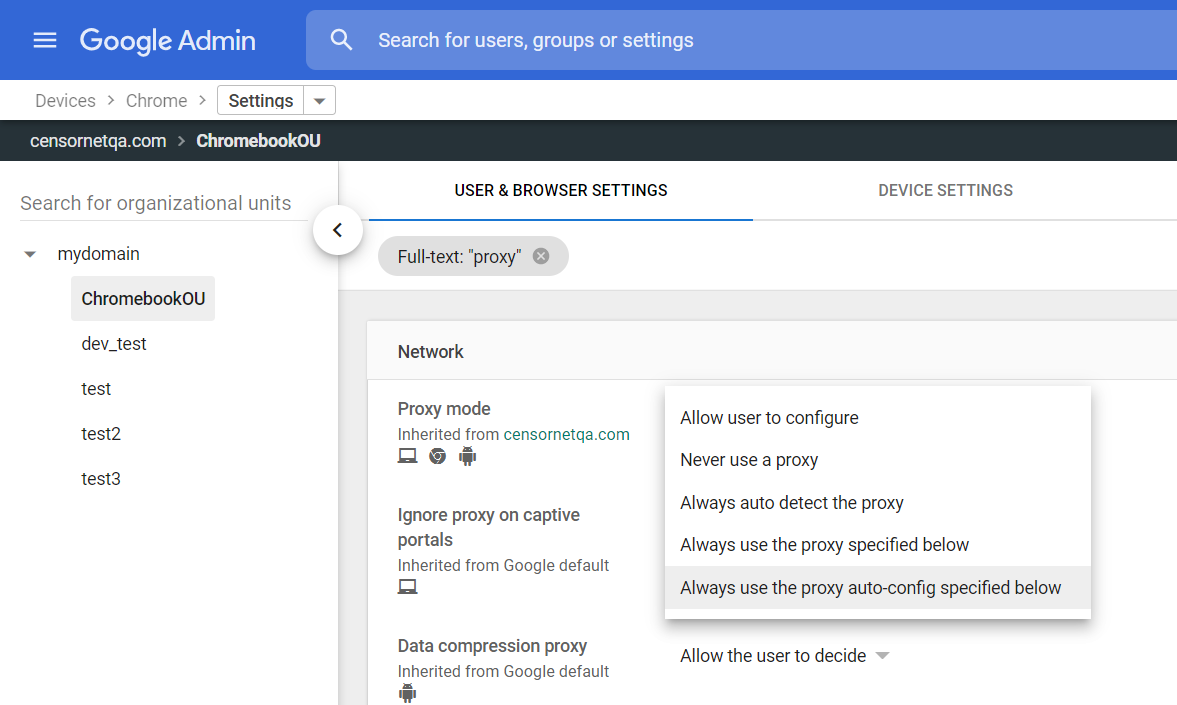
- Enter the URL
https://cl-update.cloudwebfiltering.com/chromebook/agent.pacinto the entry box provided.
- Click Save in the top right of the window.
- Swap to the main USS Dashboard and obtain the SSL Certificate from the Chromebook profile that the agent will use. Navigate to Products, Web Security and select Agent Configuration.
- Select the Default Chromebook Profile indicated with a yellow star and then the SSL Key section.
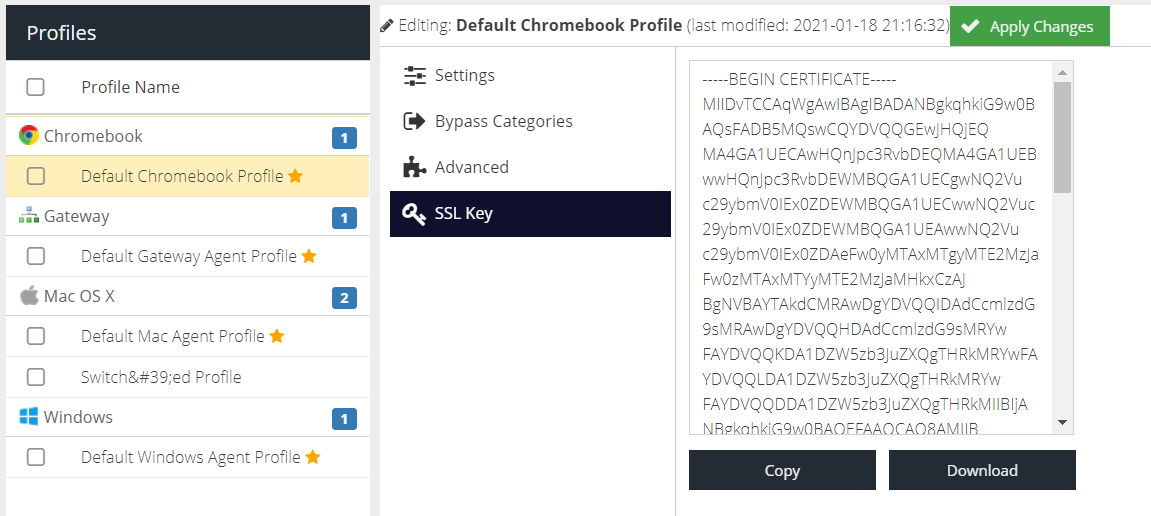
- Click Download and store the key file somewhere safe.
- Swap back to the Google Admin dashboard and navigate to Devices then Network and Certificates:
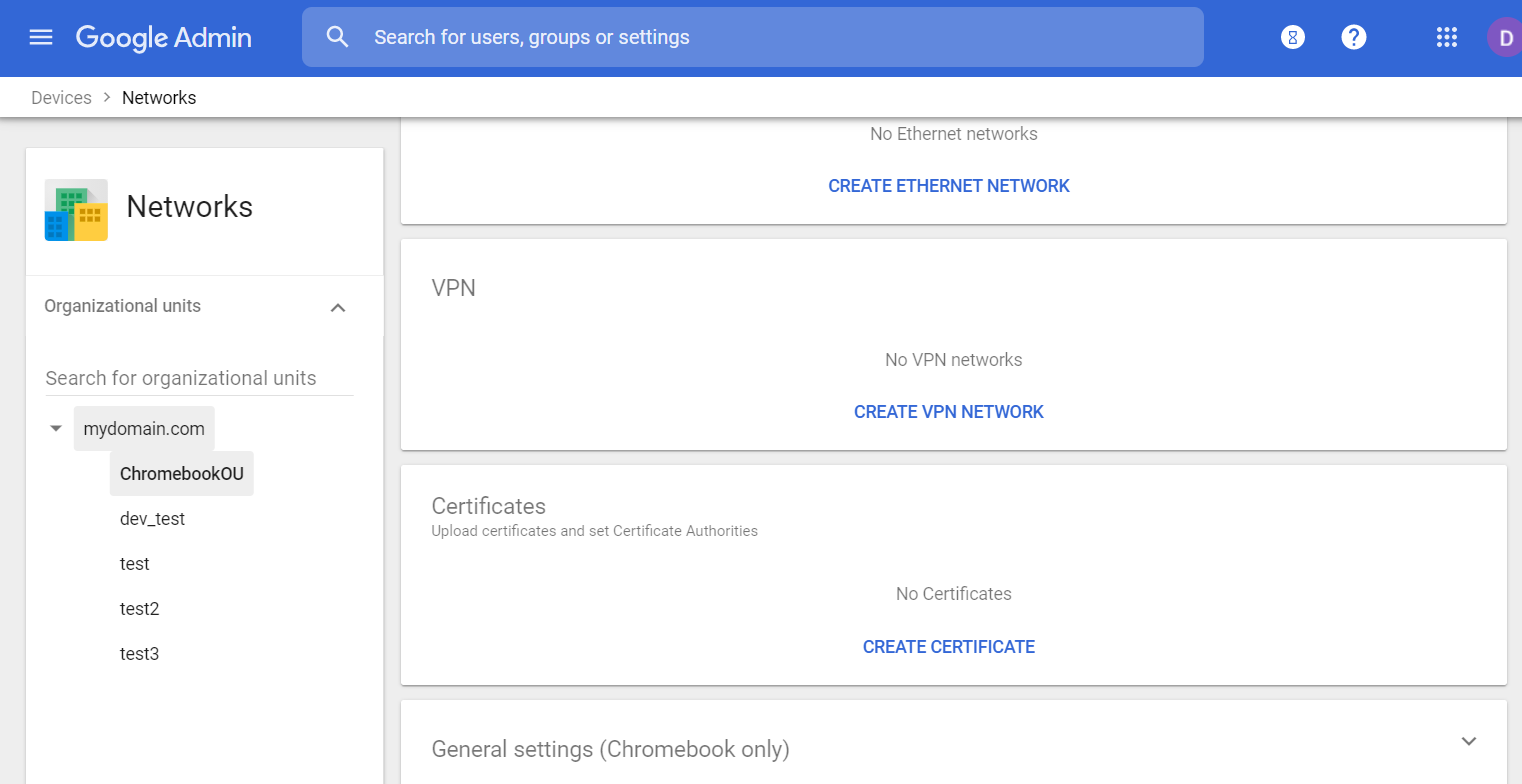
- Within the Certificates panel, click Create Certificate.
- Enter a name e.g. Chromebook SSL Intercept Certificate and then select the file downloaded in Step 16 from your computer. The file will automatically upload.
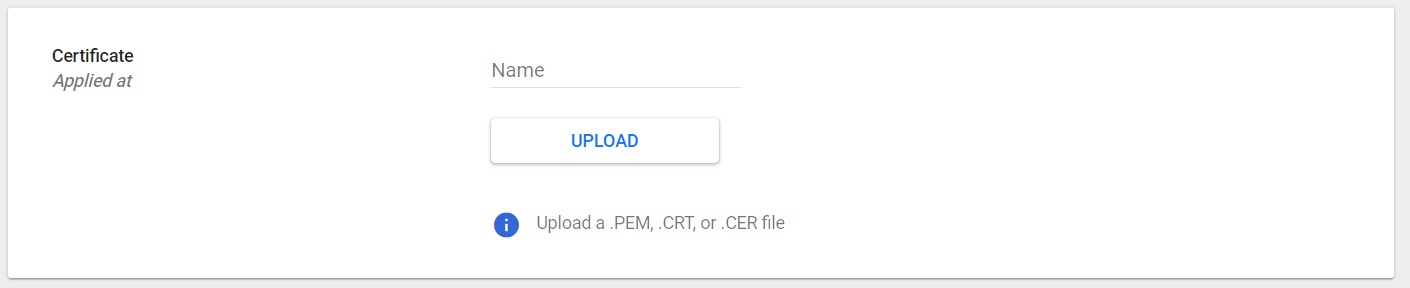
- In the Certificate Authority panel, tick Chromebook
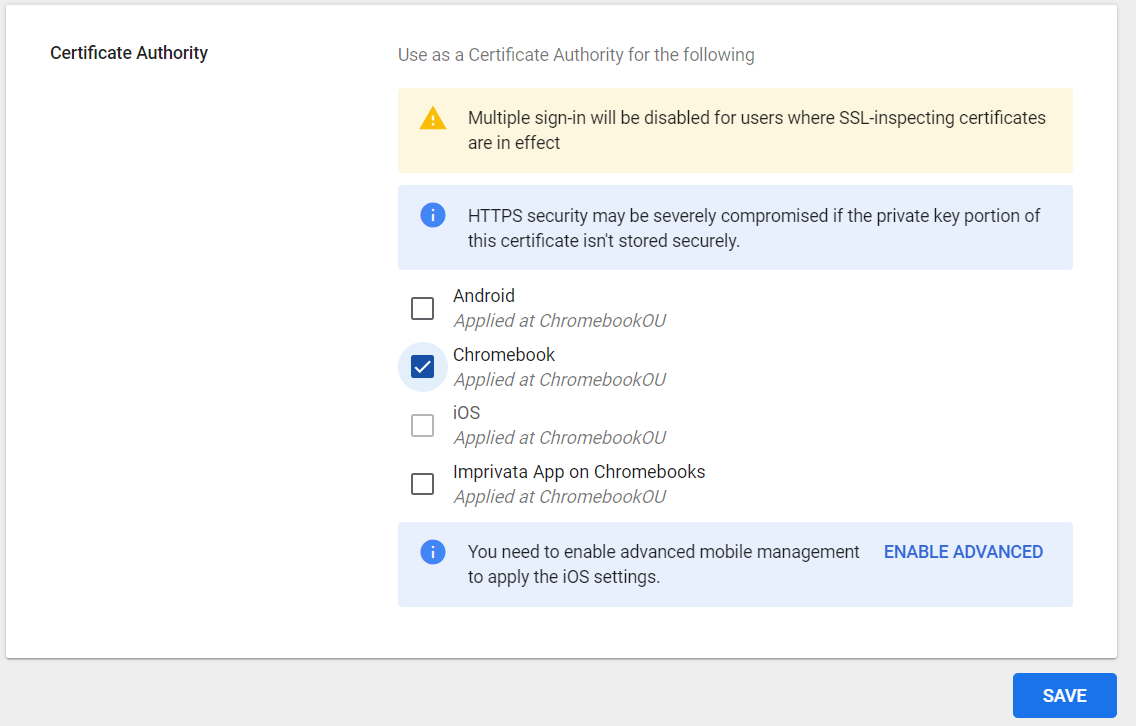
- Scroll to the bottom of the page and click Add
- Now log in to a Chromebook device using a user from the Organizational Unit configured as part of this guide. The app should automatically install from Google Play
- Open the Google Play store on the Chromebook, navigate to Apps and then Work Apps and then click the Unified Security Service icon. Click the Open button.
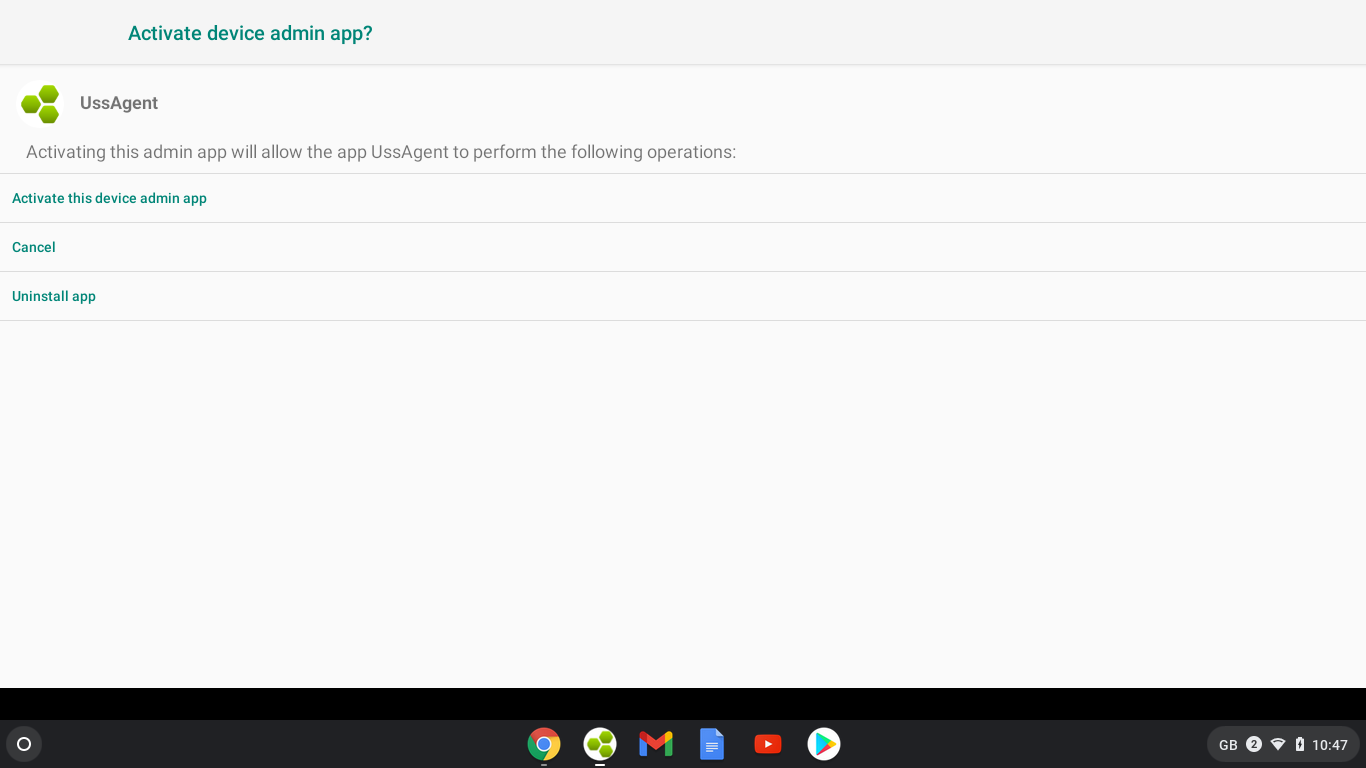
- You will be prompted to Activate device admin app?. Select Activate this device admin app.
- The app is now deployed and an entry will appear in the Deployment section within the USS dashboard:
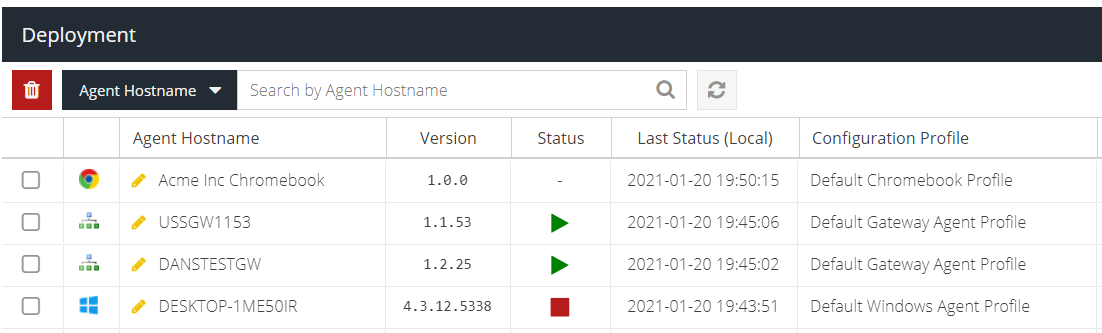
The user can now close the app and begin browsing with the Google Chrome browser. Web traffic will be filtered according to the filter rules configured in the USS dashboard.
Troubleshooting Tips
Cannot browse the web after deploying the Chromebook agent
The Chromebook user must visit the Play Store, open the USS agent app and approve it - see steps 24 and 25.
The Chromebook app status is "Installing..." in the Play Store
This is most likely due to Internet access or network connectivity.
- If you are using a custom
.pacfile, ensure that the correct bypass entries are in place (see the example .pac file). Also ensure that wherever your.pacfile is hosted it can be accessed from the Chromebook network. - Ensure that the username and password in the configuration JSON is correct in Step 9 and that at least the Agent Installer role has been assigned to the user.
- If you are still having problems, set the Proxy Mode to Never Use A Proxy and reboot the Chromebook. Login as normal and continue to approve the app in steps 24 and 25. After the agent app is installed, re-enable Proxy Mode using the default
.pacfile URL and reboot the Chromebook again.
The user has uninstalled the app and can no longer browse the web
The use of the app is enforced by Step 8. Whilst the user is able to uninstall the app, doing so without the administrator approval will simply prevent web access with a network error. Please contact your Google Admin administrator and request the app to be removed from your policy or OU.